
Increasing Cyber Security threats
As can be seen on the news worldwide, cyber attack is becoming a larger, increasingly pervasive and costly problem. As technology and industry becomes more interconnected and interdependent, the chance of a cyber attack being carried out on an individual business increases.
Forms of cyber threat are ever evolving and elaborate and they are not merely limited to external threats (with arcane words such as “phishing”, “water-holing” and “ransomware” being added to the dictionary with alarming regularity).
These threats can be launched from anywhere in the world and may well originate from apparently trusted sources, but cyber security threats also include local concerns, such as site access, unsecured connections (such as USB, Wi-Fi and Bluetooth), unintended employee actions, and simply put, theft or sabotage.
In an almost overwhelmingly complicated area, it may seem a daunting task to secure your business from attack.
However, as has been seen recently with the worldwide ransomware attacks, it is vital to do so. Businesses and organisations can be brought to a grinding halt for days or even weeks by cyber attack. The cost of recovery is not only be large financially, but can also be counted in terms of loss of reputation and customer confidence.
Countermeasures for Cyber Protection
Just as the forms of cyber attack have evolved over the years, so have the forms of countermeasure. There exist various Cyber Security standards and published materials that set out the measures that are recommended to be taken to protect the cyber environment of any organisation.
These include the standards NIST (National Institute of Standards and Technology), NERC (North American Electric Reliability Corporation), ISO/IEC 27001:2013 and many more.
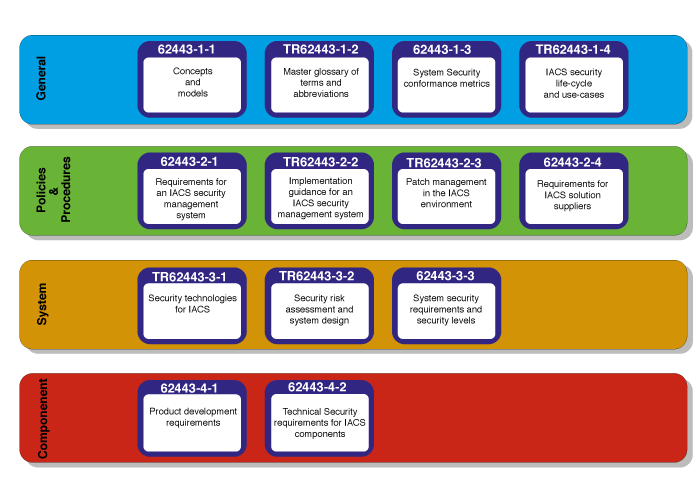
The standard applied specifically to the Controls and Automation industry is ISA/IEC-62443 (formerly ISA-99). It comprises standards, reports and procedures pertaining to cyber security in an IACS (Industrial Automation and Control Systems).
Broadly, the IACS is a collection of networks, control systems, SCADA systems and various other systems deemed to be vulnerable that require Cyber Security protection. Normally these are separated from the wider business IT network and often not protected by the measures implemented by the business IT.
Step one of the CSMS process laid out in IEC-62443 is to precisely define the IACS area.
The CSMS (Cyber Security Management System) is the core of any cyber security effort and again its scope, definition and implementation is detailed in IEC-62443.
The Asset Guardian Solution
Asset Guardian has been designed to form the back bone of a robust, integrated and user-friendly Cyber Security Management System and is compliant with IEC-62443 and other Industry Standards.
Asset Guardian Cyber Security sections are organised into Zones, Conduits and Incident Reports. These sections integrate seamlessly into the other sections of Asset Guardian such as Hardware, Software and Users.
As part of the CSMS, Asset Guardian also provides the facility to:
- Identify Cyber risk
- Organise user training
- Implement business continuity and Disaster Recovery plans
- Organise and structure personnel, physical and environmental security
- Document network segmentation
- Record Access Control (i.e Administration,/Authentication/Authorisation)
- Improve Incident respsonse
- Provide analytics to improve, develop and maintain the overall CSMS.
Asset Guardian used as a Cyber Security Management System minimises cyber security threats, greatly improves incident response and aligns your business to the IEC 62443 Cyber Security Industry Standard.
If you would like any more information on Asset Guardian, please fill out the contact form below, and a member of our team will be in contact soon.
Written by Graham Foss. As one of AGSL’s team of Technical Consultants, Graham Foss is responsible for implementing the company’s product development and technology strategy. Before joining AGSL in 2016, Graham was employed for 12 years as a lead software engineer at Aker Solutions Subsea Ltd, where he worked on projects in the North Sea, North Atlantic and Norway. Graham holds a degree in Computing from Edinburgh’s Napier University in Edinburgh, where he graduated with distinction. A Chartered Engineer, he is a member of the Institution ofEngineering and Technology (IET).



